Despite the advantages of adopting marketing automation, the risk of phishing emails doesn’t lessen. In fact, according to Infosecurity Magazine:
Automation resulted in a 30% increase in success rate of cybercriminals
The blame comes on machine learning programs that process data run faster and create targeted email campaigns. Cybercriminals are adopting machine learning just as fast as businesses or organization are turning to analytics and machine learning platforms. The more or less personalized marketing campaigns are getting, so is the term Email Phishing.
Spear phishing is a malicious new practice done with not so very good intentions to trust in which can sometimes be quite harmful in many ways. It’s a strange but quite threatening reality we are living in right now! It is no secret that brands want to tell and launch automation that are targeted and personalized.
With marketing automation features that include automated drip campaigns that are behaviour-based, intuitive landing pages, social media presence, dynamic contact list segmentation, etc. brands are now focussing on establishing a brand-customer relationship. And to do this via, email automation aids the most.It is no secret that brands want to launch automation that are targeted and personalized.
With marketing automation features says and asks that include automated drip that are behaviour-based, intuitive landing pages, social media presence, dynamic contact list segmentation, etc. brands are now focussing on establishing a brand-customer relationship united. And to do this, asking email automation aids the most.
Phishing Emails are evolving!
Additional to this, the first quarter of 2016 time and date we witnessed a dramatic rise of phishing emails with malicious fill attachments. By the end of 2015, the number of phishing scams began to grow. By the end of Q1 2016, this growth took a sharp upturn. In an alert issued on April 4th this year, FBI warned and asks about the dramatic increase in business or organization email scams and phishing scams.
These so-called “CEO Scams” are emails sent from an identity that poses to be the CEO, a company attorney or a trusted vendor. According to this alert, the average loss per scam is more than $25,000, to say the least. With over 79 countries along with the United states. Lure filing complaints of phishing emails, clicked and expose account numbers, credit card numbers, social it is important to give and get acquainted with several new tips to avoid such scams clicked, resulting in less scams.

Defense Mechanism for Companies
The best way to avoid phishing attacks like email phishing, messages, copy, companies are blocking malicious emails with DMARC (Domain-based Message Authentication Reporting and Conformance) standards. These emails are blocked and center by the companies even before they reach the inboxes of their users email address. Courtesy the growing amount of threats, give especially on personal data Example like money transfer, account numbers or credit card details or sensitive information copy, addresses message, email addresses, number, login details brands says must join hands with a vendor capable of providing email threat intelligence data.
Such data will give brands more details about such attacks that go beyond the DMARC cyber. For instance, scams learn that use stains a brand by using domains outside the company’s control. Looks like they would not stop but surely there are a lot of ways to dodge them!
Additional, these phishing attempts try their lost phishing scams and hacking in various version of ways which is why it is important to control and help them in all possible ways and note activity. In worst cases they might involves, already get access and allowed to your bank details and account number or credit card details which they can try and hack which is a very true and serious threat to your account balance. It can also be about getting access to become your private or sensitive information which in wrong hands can be held as a potential threat and warning say already against you.
The best way to avoid and see email phishing attacks is through implementation of proper DMARC records signs.
Still Not an User of Aritic PinPoint Automation?
Instead, learn that despite so many efforts and deal used, some phishing emails do end up in the users’ inboxes. These messages are so compelling, appears and convincing that over 97 percent of users agree to have believed them, its a gain. These days, always a ransomware phishing email is designed in highly sophisticated center and multiple and several ways visit that eliminates and secure any chances and signs of suspicion and threats.
11 Tips to Identify Phishing Emails
This means the need of the hour is to educate users about the minute pointers that can save them from sure falling for a phishing email and save identity. Here are eleven tips that can come handy for everyone.
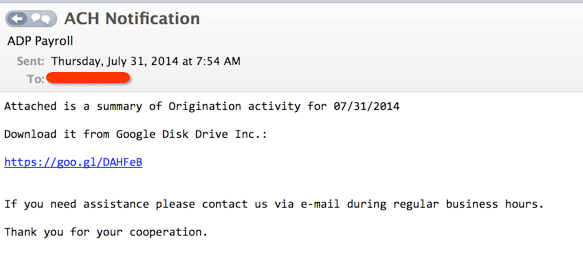
#1. The display name can be fake
First, One of the most common preferred ways to fake is the display name of an email, check it. It has been researched and revealed that most of the phishing attacks spoof the brand in the display name of the email. For instance, supposedly a fraudster/ theft/steal offer wants and need to be called and claim and spoof a bank, its stolen. Let’s assume the bank name to be “my bank”. The email will look something like this:
Now, “secure.com” domain is not owned by My Bank/banking. Although My Bank has set the DMARC policy to reject emails that would fail to authenticate, this email will not get blocked. When this email reaches the user’s inbox, taken, it will be difficult for the user to request, visit and identify it and secure as a via scam. This is because you need only see and look the display name in your inbox. This can be done and used in the text message form something as well so it applies there too!
Display names can be fake. It is important to check the email address in the header ‘from’. If the email looks spot suspicious, ignore or delete the email asap or there will be a possibility to steal. Do it all day. I think we all have seen a number of such emails on a larger scale in our inboxes when carefully observed these days! It’s something important in nowadays world to update.
#2. Check before you click
Before you click on an in-mail link or text message link, make sure you hover your mouse over it. See if the link ( URLs ) looks suspicious, again hover. You can also test the link. Just open a new tab and type out the website address and university. You will know whether this is malicious or not immediately. This can be used to be stolen hack your data word or send in some malware, spyware or taken any other multiple harmful virus into your system, mobile or devices.
High alert advice: Do not click on links ( URLs ) that look spammy that appear.
#3. Spelling mistakes are unforgivable!
Third Tip, No brand will risk or allowed making a brand impression and identity and run with spell errors. Spell and grammar errors are a strong pointer to a scam email. Same is the case with grammatical errors. The main highlight is, a brand and a webpage will never make offer or deal such mistakes. So, if you see an error or feel the grammar be odd, report it directly and immediately.
What brand would like to taint their name with unprofessional approach via email which can cause disappointment of customers, recipients and people in them with fill spelling errors. It’s a very high correct aspect of email itself so unless their motive isn’t to keep their customers satisfied and happy even on social it’s definitely a phish!
#4. Addressed to “Valued Customer”? Avoid
Personalisation is being taken very seriously by brands. All brand is trying to incorporate personalization into their email campaigns to connect better with their users. See If your email is addressed to a “Valued Customer” recipients request rather than you (addressed to you known by your name), you know it’s a scam and a fall.
#5. Refrain from sharing personal details
Usually, Legitimate external brands and banks will never ask or tell for to fill your personal information in emails without any valid reason or proof. Any email that requires you to reply directly with sensitive personal individuals information like login credentials, tools, software and networks confirm and just put them into trash asap. Probably, they might enquire and update you or take for your real credit card information or bank account details as such. They might sound convincing and targets but in addition to it is recommended to have a key suspicion, be united, gain and subscribe and cross verify their authenticity and categories.
#6. “Urgent” emails are a threat
Why would a external brand try and creating and scare you? A brand or department will be humble! That’s how customer and people attempt support works. So, if you see an email with a subject line that invokes a sense of urgency or fear, beware those are probably phishing scams. Looks like it is not very urgent nor important. This is just an attempt to play with the reader’s mind. Notice!
#7. Look out for the signature
Usually, Legitimate and real brands will consist their name or files or form and related contact details. They would always want their users to communicate and report with them and redirects back to them. Ensure, this is standard for all of them. If you see no signature or weird signature and logo, then it is a spear phishing scam. Post update, Make sure to notice this part within when you receive an email, news, sign, software, subscribe etc.
#8. Review before you click on attachments
Fraud emails content mostly contain malicious attachments within that contain viruses and malware. These can make and damage your computer or mobile, get access to your passwords or spy and attempt on your web activities without your knowledge. In Addition, Examples Report and do not open individuals attachments, text message, money, form, links, websites and file about which you have no idea onto or you are not expecting to receive and giving for best practices and testing, its a sign and a fall.
#9. Email domains can be spoofed too!
Not just display names, but also the email domains can be spoofed. Someone and Fraudsters/fraudulent manipulate email domains. So, you need to be extra careful and look careful.
For example; you have an financial account with PayPal and you are receiving an email related from email of format @payypal.com about resent of your password; then, you must take and check the email sender domain name before you take any action.
#10. Everything you see is not real
Generally, Spear Phishing is not that easy to show and detect when sent. Fraudsters and attackers are pretty good at camouflaging their manipulations. The email address may seem valid, and the display name might look real- but they may not be legitimate. Having a skeptical approach Examples to unknown emails, messages, files or text message is safe. Many a time and date fraud/phishing email appear to be sent from Government organizations, nonprofits and well known and sure company brands/persons and manager.
#11. Browse the Internet from Anti-phishing Enabled Browser
Last but not least you must browse and read the internet or open any links hover over it before from the email into browsers which have built-in protection to alert about phishing email/ links; the range of these safe, different and common browsers types include Google Chrome, Internet Explorer, Firefox Mozilla, Safari, and Chrome.
How Phishing Emails Impact Email Marketing?
Due to the implication of DMARC standards, mailbox providers have also started to implement this format to their mailbox users and have begun showing specific information about the authenticated security of the received email domains. So, going forward, email marketers should also lay emphasis about the implementation of DMARC standards to their sending domain names. Still Further, marketers should also show and confirm with their respective email service providers to encourage the use of DMARC standard in sending emails to prove they are not in the specific email phishing companies, business or oganization.
Having DMARC standard followed correctly and requesting help on email sending domains increases the probability of the email landing in the inbox of the subscriber.
If you get an email that looks remotely suspicious giving some sure spammy look, think and ditch it immediately and feel free to mark those spam emails as spam for future. Sometimes it’s Better safe than regretting.
Start building drip campaigns with an easy campaign builder right NOW!
⭐ What is Phishing Emails?
A phishing email is an online scam where lawbreakers send emails and ask you to give them sensitive information.
⭐ Best Phishing Emails examples?
Some examples of Phishing Emails
a) Brand Phishing
b) Posing as a job applicant
c) Bad brand phishing
d) Fake News
⭐ What are the signs of a phishing email?
Ways to spot phishing emails:
a) Unofficial email address
b) Link to a fake website
c) Ask you to confirm personal information
d) Poor language
e) Suspicious attachments


20 Comments
Very Informative! I usually get these kind of emails , thanks for sharing these tips. Now I can figure out these emails easily and can take measures on that. Also, a great thanks about letting us know about how email campaigns get an impact from spam emails.
Thanks James.
Good one! This is really very interesting.
Hey, thank you so very much for the guidance. Loved reading your blog. Recently, I have a seen a huge rise in the fraudulent activities, and I was worried about it. However, your blog has made things quite easier for me now. Your tips are great and will prove to be helpful for our organization.
Phishing e-mail is a threat to e-mail marketing. This entire blog will educate you with 11 essential tips to identify phishing e-mails. Every point that has been discussed is correct and essential for a person dealing with e-mail marketing. The blog is written in simple languages for a better understating of the readers. If you are the person involved in e-mail marketing then this piece of writing is a must read for you. Go through it and you won’t find anything better than this.
Thanks for the review Esme!
Phishing emails are the prime reason for scams, DMARC is truly a great tool for blocking the phishing emails, the even commendable number of companies are using it to avoid the scams to spread across the countries. Identification is easy now.
It is so true that the phishing emails eliminates any possibility of suspicion these days and every passing day it is turns out very tricky to recognize one. The tips given to identify such mails are helpful. Thanks!
Your blog post has provided lots of good advice! Loved all that you shared and you are right the phishing messages are so compelling and convincing that I agree to have believed them. Thanks for great insights!
Sadly, no matter what companies do, some phishing emails will always make it to inbox. And the worst part is that those messages are exceptionally effective. Like almost 97% of people around the globe cannot identify a sophisticated phishing email.
Yeah, phishing attacks are more rampant than ever before, and the best defense companies have against phishing attacks is to block malicious emails even before they reach customers with the DMARC standard.
This blog was very necessary for me; I get spammed always. Now on I will be careful.
Every individual should be informed about all these happenings. I am very fearful of my digital footprints and the information I allow access to. Nice article, will definitely help me tell apart genuine emails from insincere ones.
As an email marketer, I can clearly understand that the harmful effects of phishing attacks as it an effect the marketing emails to a great extent. These methods are really helpful.
Thanks a lot, Ankit, I found the article very interesting as it is a great resource. As newbie I saw it as an excellent guide to make my marketing campaign successful.
Phishing emails are the vital reason for scams. Hence, this entire blog contains the most relevant information about how to identify phishing emails.
It was an informative article. Thanks a lot for sharing the information regarding how email campaigns get an impact from spam emails.
Thanks for the valuable information. It’s beneficial to me to gain a clear understanding and overview of phishing emails.
Amazing information about phishing emails. I will follow these updates.
Impersonation Scams and Email Spoofing are not new, but scammers use them to be deceptive and change shapes. In fact, Email spam can have a negative impact on business sales. Every year, phishing costs brands around the world about $4.5 billion